On December 4, 2025, a 17-year-old individual was taken into custody in Osaka in accordance with Japan’s Unauthorized Access Prohibition Act for illicitly accessing the personal information of more than 7 million users of Kaikatsu Club, Japan’s leading internet cafe chain. The culprit admitted that his motive behind the breach was to purchase Pokémon cards.
Although this incident follows a somewhat typical narrative seen since the 1990s involving tech-savvy individuals like Kevin Mitnick, whose technical skills surpassed their ethical judgment, leading them into high-profile cybercrimes driven by a desire for recognition, financial gain, or thrill-seeking, there is a unique aspect to this case: the perpetrator lacked technical expertise.
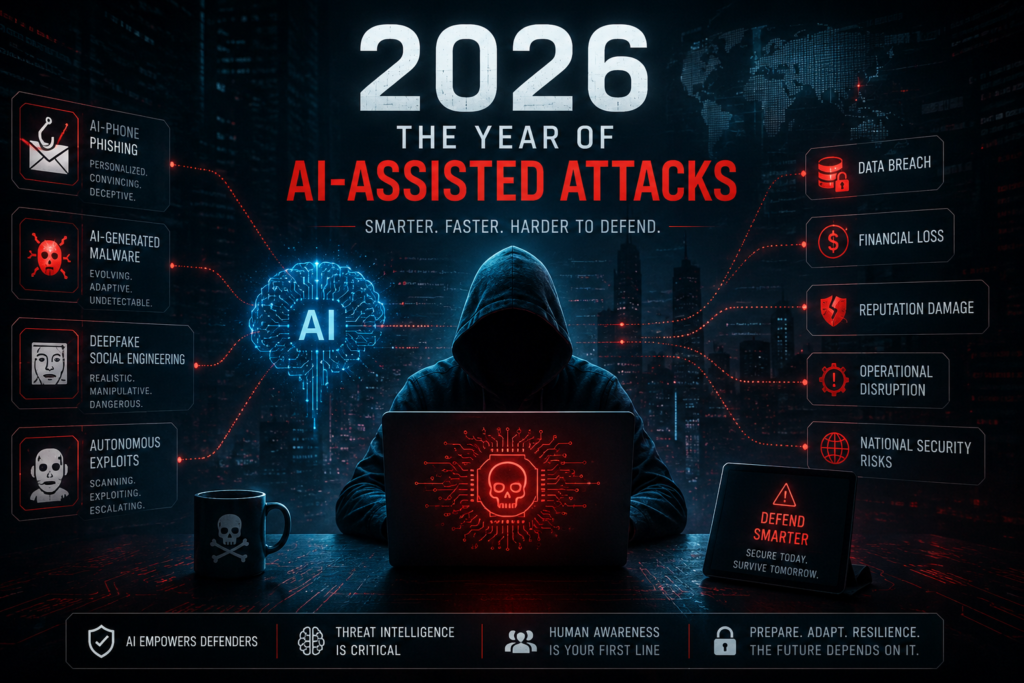
In the year 2025, advancements in AI-backed chat and agent systems marked a significant advancement, transitioning from imperfect coding aids to highly effective coding tools. During this period, various indicators of cybercrime frequency and severity nearly doubled. Instances of malicious software found on public platforms rose by 75%, cloud breaches increased by 35%, and AI-generated phishing surpassed the effectiveness of human red teams. Notably, the characteristics of those involved in cyber attacks underwent a notable change.
In February 2025, three teenagers aged 14 to 16 without coding backgrounds utilized ChatGPT to create a tool that targeted Rakuten Mobile’s system around 220,000 times, using the proceeds for gaming consoles and online betting. In July of the same year, an individual leveraged Claude Code, an advanced agentic coding platform, to carry out an extortion scheme against 17 organizations over one month. This involved using agentic AI to develop malicious code, categorize stolen data, analyze financial records for ransom demands, and compose extortion messages. Subsequently, in December 2025, another person employed Claude Code and ChatGPT to breach multiple Mexican government agencies and steal over 195 million taxpayer records.
While such attacks were feasible prior to 2025, what is now evident are single individuals executing operations that previously required organized groups and non-technical individuals conducting smaller-scale attacks that would have typically been associated with skilled hackers or engineers before the era of AI. The year 2025 saw a significant reduction in the barriers to executing technically sophisticated cyber attacks.
Throughout 2025, various metrics concerning bot activity, malware instances, targeted infiltrations, and phishing attempts showed substantial increases alongside remarkable progress in LLM capabilities on technical standards.
According to data from Sonatype in 2022, there were around 55,000 malicious packages on public repositories which surged to approximately 454,600 by 2025. Notable spikes occurred in both 2023 (following GPT-4’s launch) and in 2025 (a pivotal year for agentic coding).
Another crucial metric reflecting real-world attacker prowess is time-to-exploit which has undergone drastic changes from the pre-AI era. This metric gauges the duration between when a vulnerability is disclosed publicly and when an exploit for that vulnerability is detected “in the wild.”
From over 700 days in 2020, time-to-exploit plummeted to only 44 days by 2025. This indicates that malevolent actors are developing exploits for known vulnerabilities within two months rather than almost two years as previously observed. Surprisingly, Mandiant’s M-Trends report for 2026 revealed that time-to-exploit has essentially become negative – exploits are now frequently deployed before patches are released with approximately 28.3% of CVEs exploited within just one day of disclosure.
The performance levels of cutting-edge models such as ChatGPT, Claude Code, and Gemini on tests like SWE-bench escalated significantly across late-2024 through early-2026. By December 2025 alone, top models were able to resolve nearly 81% of authentic GitHub issues presented on these assessments.
The evolution of AI-assisted coding reached a crucial juncture towards late-2024 and particularly during 2025. While this advancement turbocharged coding capabilities significantly; it also bolstered offensive potentials leading to increased frequency and severity of cyber assaults witnessed in the subsequent year.
AI technologies have accelerated both defensive and offensive strategies; however recent data from years ’25-’26 show an inclination favoring attackers within this escalating arms race. The average duration required to address identified high-risk or critical vulnerabilities has extended to around 74 days as per Edgescan’s Vulnerability Statistics Report for ’25 with approximately half of vulnerabilities within large company systems remaining unmitigated.
Moreover, organizations are grappling with heightened risks stemming from increased malware infiltrating public package repositories. For instance; the Shai-Hulud attack targeting npm ecosystem in September ’25 compromised over five hundred packages resulting in exposure of sensitive information from over four hundred organizations alongside theft amounting to $8.5 million following exploitation via Trust Wallet’s Chrome extension due to exposed credentials misuse prompting several entities to enact temporary code freezes post-incident.
This predicament is exacerbated by detection challenges encountered within npm ecosystem where nefarious packages masquerading as popular libraries managed eluding conventional scanning techniques due largely to their deceptive resemblance with legitimate modules both structurally & functionally likely facilitated by AI technology as noted by Chainguard CEO Dan Lorenc pointing towards organizational limitations when managing increasingly complex & widespread vulnerabilities autonomously.
The overarching lesson derived from ’25 underscores the inevitability of such attacks outpacing conventional defense mechanisms given shrinking time frames for countering exploits vis-a-vis rapid malware advancements evading traditional detection tools relied upon historically by organizations. The expanding overlap between potential perpetrators possessing both intent & capability previously reserved for elite hackers signifies evolving threat landscape amidst accelerated software proliferation setting stage for more potent supply chain breaches anticipated by ’26 & beyond leveraging enhanced model capabilities subsequently raising concerns about future security implications.
Relying solely on speed or evasion tactics may prove insufficient amidst current circumstances thus advocating instead for proactive measures aimed at eliminating entire classes of vulnerabilities thereby allowing teams greater focus on residual risks as demonstrated by Chainguard Libraries initiative reconstructing open-source libraries from verified sources seeking structural immunity against prevalent attack vectors like CI/CD hijacking or package distribution fraud safeguarding users effectively.
Chainguard Libraries successfully thwarted nearly all malicious npm packages tested totaling at an impressive rate of over ninety-nine percent along with comparable results against roughly ninety-eight percent of malicious Python packages assessed reflecting their efficacy against prevalent cyber threats demonstrative of their potential utility within organizational defense strategies moving forward.
The surge observed last year comprising four hundred fifty-four thousand six hundred malicious packages followed by close to four hundred thousand throughout a single quarter underscores accessibility & affordability enhancements afforded by tools enabling aforementioned attacks emphasizing imperative need for robust defense mechanisms pre-emptively mitigating impending threats ensuring holistic protection while adapting proactively against evolving cyber risks influencing operational paradigms across sectors facing mounting cybersecurity challenges warranting strategic reevaluation encompassing novel approaches emphasizing prevention over reactive countermeasures essential towards fortifying digital resilience amidst shifting threat landscapes heralded under AI-driven technological advancements disrupting status quo governance frameworks necessitating adaptive responses aligned with dynamic security imperatives perpetuated across digital ecosystems shaping future cybersecurity endeavors amid escalating adversarial landscapes shaping strategic cybersecurity imperatives warranting agile remedial actions reinforcing commitment towards enhancing digital defenses sustainably safeguarding critical infrastructure resilience enduringly amidst pervasive threats unfolding rapidly across global information landscapes demanding collaborative vigilance concerted efforts fostering collective security resilience resilience fortifying organizational defensive postures against emerging threats facilitating swift mitigation responses bolstered tamper-proof security frameworks adapting dynamically towards sustainable adaptive security
